Welcome to our Little Black Book, an inspirational series of business stories and insights from our brilliant members.

Paul Marsh on securing information
CEO - SecQuest
Paul morphed his enthusiasm for technology into a professional career in the 90s (the birth of alternative media) and the 00s (when the Internet grew from covering 6.7% to 25.7%), by working in computer services for the IBM brand and becoming a key member of IBM’s X-Force ethical hacking team for over a decade.
Technical security is Paul’s expertise; he established his Cyber Security Penetration Testing Service at SecQuest in 2012; SecQuest is a trusted advisor, who delivers Cyber Security Services to many household name businesses, across multiple industry sectors.
Do you want more articles like this in your inbox? If so then register below...

Discover more of their secrets of success

Jarid Hixon
Read more
Cosmic Carrot
Read more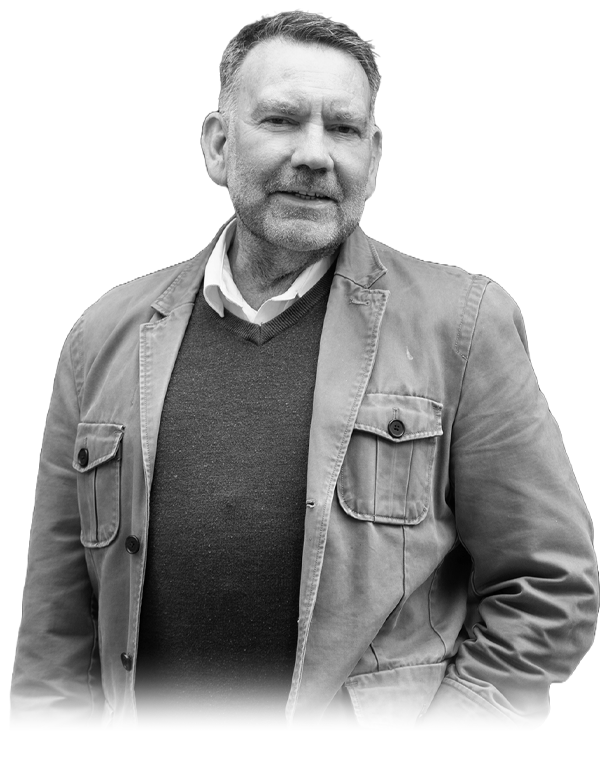
Nick Maguire
Read more
Ben Cross
Read more
Josh Chapman & Akis Zissis
Read more
Alec Smith
Read more
Gary Frost
Read more
Kelly Bruton
Read more
Josh Mitchell
Read more
Ashley Benfield
Read more
Mike Keats
Read more
Gary Light
Read more
Faye Williams
Read more
Victoria Hamilton
Read more
Phil Moulds
Read more
Rich Cook & Andrew Morgan
Read more
Raveen Sandhu
Read more
Daniel Sagar
Read more
Jon Craddock
Read more
Coran Stubbington
Read more
Marc Bishop
Read more
Scott Rae
Read more
Rich Webley
Read more
Justin Neale
Read more
Heather Pierpoint
Read more
Dan Shilcock
Read more
Ben Pike
Read more
Drew Patel
Read more
Wayne Freebody
Read more
Victoria Sedgley
Read more
Victoria Chapman
Read more
Debbie Moreton
Read more
Louis Lawrence
Read more
Dan Green
Read more
Sarina Mann
Read more
Mikaela Jubb
Read more
Chelsey & Joe Terrey
Read more
Richard Browning
Read more
Neil Lewis
Read more
Ashley Fernandes
Read more
Chris Ward
Read more
Paul Clarke
Read more
Verity Lovelock
Read more
Xavier Fiddes
Read more
Graham Bell
Read more
Dan Loveridge
Read more
Darren Jacobs
Read more
Glen Crump
Read more
Simon Hawtrey-Coombs
Read more
Lawrence Bath
Read more
Rachel Young
Read more
Neil Kerr
Read more
Dan Gateshill
Read more
Callum Donnelly
Read more
Andy Hooper
Read more
Shaun Ramazannezhad
Read more
Darren Brown
Read more
Kevin Briscoe
Read more
Paul Sams
Read more
Colin Buchan
Read more
Jamie Southall
Read more
Paul Phelps
Read more
Spencer Bowman
Read more
Donovan Long
Read more
Steve Cole
Read more
Luke Newman
Read more
Zoe Hanson
Read more
Damian Gevertz
Read more
Sally Golden
Read more
Matt Sanger
Read more
Jeremy Robbins
Read more
Nella Pang
Read more
Andy Hollands
Read more
Sam Griffiths
Read more
Alex Hurn
Read more
Zoie Golding
Read more
Ross Breckenridge
Read more
Richard Allen
Read more
Jon Martin
Read more
Steve Crawford
Read more
Louis Cross
Read more
Ian Riggs
Read more